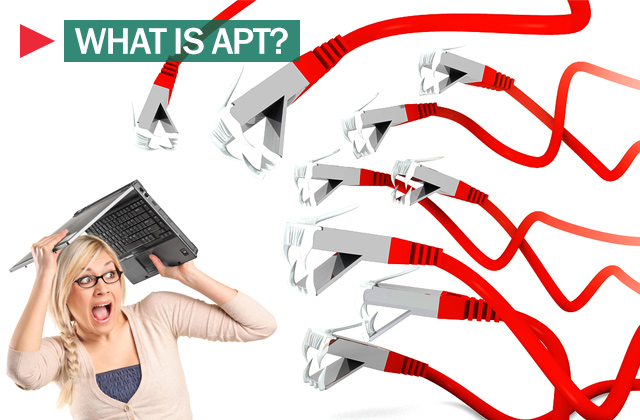
In cyber security, there are a vast number of malicious threats. Many of these threats write malware, though there are plenty of other ways for cybercriminals to be malicious. The skill level between them varies a lot, though. Many “hackers” are just script kiddies, only able to run existing tools and to lack the skills to make their own. Many hackers have the skills to make their malware, though the exact caliber varies wildly. There is one more exclusive tier, though, the APT.
APT stands for Advanced Persistent Threat. They are the cream of the crop for hackers and are generally the best in the business. APTs aren’t just technically skilled in exploit development; they also employ a range of other skills, including subtlety, patience, and operational security. Generally, it is assumed that most, if not all, APTs are nation-state actors or at least state-sponsored. This assumption is built from the time, effort, and dedication they show in achieving their goal.
Fingerprints of an APT
The precise aims of an APT vary by country, APT, and attack. Most hackers are motivated by personal gain and so break in and try to grab as much valuable data as quickly as possible. APTs perform sabotage, espionage, or disruptive attacks and are generally politically or sometimes economically motivated.
While most threat actors are typically opportunistic, APTs tend to be quiet or even very targeted. Rather than just developing exploits for vulnerabilities they find, they will identify a target, work out how best to infect them, and then research and develop an exploit. Typically, these exploits will be very carefully configured to be as quiet and subtle as possible. This minimizes the risk of detection, meaning the exploit can be used on other chosen targets before it is discovered and the underlying vulnerability fixed.
Developing exploits is a technical and time-consuming business. This makes it an expensive business, especially when dealing with highly complex systems without known vulnerabilities. As nation-state funds are available to APTs, they can typically spend a lot more time and effort identifying these subtle but severe vulnerabilities and then developing extremely complex exploits for them.
Attribution Is Hard
Attributing an attack to any one group or nation-state can be difficult. By performing deep dives into the actual malware used, the supporting systems, and even tracking targets, it can be possible to link individual strains of malware to an APT fairly confidently and to link that APT to a country.
Many of these highly advanced exploits share bits of code from other exploits. Specific attacks may even make use of the same zero-day vulnerabilities. These allow the incidents to be linked and tracked rather than as a one-off, extraordinary malware.
Tracking many actions from an APT makes it possible to build up a map of their chosen targets. This, combined with a knowledge of geopolitical tensions, can at least narrow down the list of potential state sponsors. Further analysis of the language used within the malware can give hints, though these can also be faked to encourage misattribution.
Most cyber-attacks from APTs come with plausible deniability because no one owns up to them. This allows each responsible nation to perform actions it wouldn’t necessarily want to be associated with or accused of. Because most APT groups are confidently attributed to specific nation-states, and it’s assumed that those nation-states have even more information to base that attribution on, it’s reasonably likely that everyone knows who is responsible for what. If any nation officially accused another of an attack, they’d likely be on the receiving end of a retaliatory attribution. By playing dumb, everyone gets to keep their plausible deniability.
Examples
Many different groups name APTs other things, which complicates tracking them. Some names are just numbered designations. Some are based on linked exploit names are based on stereotypical names.
There are at least 17 APTs attributed to China. An APT number, such as APT 1, refers to some. APT 1 is also specifically PLA Unit 61398. At least two Chinese APTs have been given names featuring dragons: Double Dragon and Dragon Bridge. There’s also Numbered Panda and Red Apollo.
Many APTs attributed to Iran feature “kitten” in the name. For example, Helix Kitten, Charming Kitten, Remix Kitten, and Pioneer Kitten. Russian APT often features bear names, including Fancy Bear, Cozy Bear, Bezerk Bear, Venomous Bear, and Primitive Bear. North Korea has been attributed to three APTs: Ricochet Chollima, Lazarus Group, and Kimsuky.
Israel, Vietnam, Uzbekistan, Turkey, and the United States have at least one attributed APT. A US-attributed APT is called Equation Group, which is believed to be the NSA’s TAO or Tailored Access Operations unit. The group gets its name from the name of some of its exploits and its heavy use of encryption.
Equation group is generally regarded as the most advanced of all APTs. It is known to have interdicted devices and modified them to include malware. It also had multiple pieces of malware that were uniquely capable of infecting the firmware of hard drives from various manufacturers, allowing the malware to persist across complete drive wipes, operating system reinstalls, and anything other than drive destruction. This malware was impossible to detect or remove and would have required access to the source code of the drive firmware to develop.
Conclusion
APT stands for Advanced Persistent Threat and is a term used to refer to highly advanced hacking groups, generally with alleged nation-state links. The level of skill, patience, and dedication shown by APTs is unmatched in the criminal world. Combined with the often political targets, it’s pretty clear these aren’t your average hacking-for-money groups. Rather than going for loud data breaches, APTs tend to be subtle and cover their tracks as much as possible.
Generally, the average user does not need to worry about APTs. They only spend their time on targets that are particularly valuable to them. The average person does not hide secrets a nation-state considers valuable. It’s only bigger companies, especially those that do government work, and particularly influential people that are realistically at risk of being targeted. Of course, everyone should take their security, as well as their company’s security, seriously.
The general view in the security world, however, is that if an APT decides you’re interesting, they will be able to hack your devices somehow, even if they have to spend millions of dollars of time in R&D. This can be seen in the few instances of malware being carefully designed to jump “air gaps” such as the Stuxnet worm.
For more such interesting article like this, app/softwares, games, Gadget Reviews, comparisons, troubleshooting guides, listicles, and tips & tricks related to Windows, Android, iOS, and macOS, follow us on Google News, Facebook, Instagram, Twitter, YouTube, and Pinterest.